
MNO Core Network Solution Provider: Building Future-Ready Mobile Networks
2026-05-12
Mobile networks are evolving faster than ever. Can your core network keep up? As a dedicated MNO core network solution provider, IPLOOK delivers future-ready architectures that turn tomorrow's challenges into today's opportunities.
Architecting the Core for Tomorrow's Data Surge
The quiet hum of a data center masks a frantic race against time. Every millisecond, a torrent of structured and unstructured information floods in from sensors, applications, and user interactions. To keep pace, the fundamental blueprint of compute and storage must evolve. We can no longer simply bolt on capacity—it’s about weaving scalability into the fabric of the architecture, anticipating not just growth but the very shape of the data to come. This means moving beyond monolithic designs toward composable, software-defined fabrics that flex in real time.
Traditional spine-leaf topologies and monolithic storage arrays buckle under unpredictable spikes. Instead, tomorrow’s core relies on disaggregated resources—pools of compute, memory, and storage that can be orchestrated dynamically. By decoupling hardware from the intelligence that governs it, we transform rigid racks into fluid systems. The result is an infrastructure that doesn’t just scale out but also adapts its behavior to the workload, whether that’s a sudden burst in IoT telemetry or a sustained AI training run.
Yet the real secret isn’t in the silicon—it’s in the software abstractions that make hardware melt away. An intelligent control plane, informed by predictive analytics, can pre-empt congestion and rebalance loads before users sense a stutter. By treating the core not as a static collection of boxes but as a single, programmable entity, we create a foundation that can handle not just tomorrow’s data surge but the one ten years after that.
Seamless 5G Integration Without the Growing Pains
Moving to 5G often feels like a balancing act between staying ahead and avoiding operational hiccups. Many network operators face rough transitions, where the promise of faster speeds gets tangled in compatibility issues and budget overruns. The trick is to approach integration as an evolution rather than a revolution, keeping existing infrastructure humming while quietly introducing new capabilities.
Instead of a hard cutover, phased rollouts let you test 5G in targeted areas, gather real-world feedback, and fine-tune without disrupting service for the entire user base. Vendor-agnostic planning and software-defined networking also help, allowing older and newer equipment to work together more smoothly than ever before. The result is a network that grows its capacity naturally, almost like adding lanes to a highway without closing the road.
By the time the full upgrade is complete, customers barely notice the change—except for markedly better performance. And that’s the point: the best transitions are the ones that happen in the background, keeping day-to-day life and business running without a hitch.
Cloud-Native Agility: Scaling Networks on Demand
Modern infrastructure demands network capabilities that expand and contract with the pulse of application traffic. Rather than relying on rigid, pre-provisioned topologies, cloud-native approaches treat network functions as dynamic, software-defined resources. This shift allows teams to spin up new segments, adjust bandwidth allocations, or introduce service chains in seconds, responding directly to real-time conditions instead of waiting on manual change windows. The result is a fabric that breathes with your workloads, eliminating overprovisioning and the friction of traditional networking.
Scaling on demand isn’t just about raw capacity—it’s about context-aware connectivity. In a cloud-native stack, networking becomes an extension of the orchestration layer, where policies and identities travel with workloads across clusters and regions. When a microservice instance scales out, its network posture—security groups, routing rules, observability hooks—propagates automatically, maintaining consistency without human intervention. This tight coupling between compute and network scaling ensures that performance and compliance keep pace, even as environments fluctuate between steady state and peak demand.
Intelligent Automation: Zero-Touch Operations, Maximum Uptime
Manual tasks often eat up hours that could be spent on more valuable work. Intelligent automation steps in to handle routine processes without anyone needing to click a button. From initial setup to ongoing adjustments, the system learns patterns and acts on them, cutting out the small slipups that happen when people handle repetitive steps. This shift doesn’t just speed things up—it lets teams focus on improvements that actually make a difference.
Keeping everything running around the clock isn’t about reacting faster when something breaks. It’s about catching issues before they ever disrupt service. With tools that monitor in real time and respond automatically, potential failures get addressed quietly in the background. Self-healing routines reroute workloads, recalibrate resources, and alert the right people only when a human touch is genuinely needed. The result is fewer interruptions and a lot less noise.
What ties this together is how seamlessly these pieces fit into daily operations. Instead of bolting on another dashboard or generating more alerts, the automation works behind the scenes to keep systems steady. Over time, patterns become clearer, adjustments happen faster, and the whole setup grows more resilient without constant oversight. It’s a practical way to build reliability into the core of how things run, rather than chasing problems after they’ve already caused damage.
Security by Design: Shielding the Core from Evolving Threats
True resilience in modern systems isn’t added after the fact — it’s woven into the fabric of the architecture. When we talk about shielding the core from evolving threats, we mean building a foundation where every component, every data flow, and every access point is designed with the assumption that breaches will be attempted, and some might succeed. This mindset shifts the focus from perimeter defense to intrinsic protection: hardening the kernel, isolating critical services, and ensuring that even if one layer is compromised, the damage is contained. It’s about making the core unattractive and impenetrable, not just putting up higher walls.
The challenge lies in staying ahead of threats that morph faster than traditional update cycles. Attackers are constantly refining their methods, so the design must be adaptive — incorporating live monitoring, real-time anomaly detection, and self-healing mechanisms that respond to irregularities without human intervention. This means embedding security hooks directly into the codebase, using immutable infrastructure patterns, and rigorously applying least privilege across all interactions. The core stops being a static target and becomes a dynamic, self-aware entity that can sense and neutralize intrusion attempts before they escalate.
Ultimately, this approach reduces the attack surface to a minimum and forces adversaries to overcome multiple, overlapping barriers that are deeply integrated into the system’s logic. It’s not merely about encrypting data or patching vulnerabilities; it’s about rethinking how components communicate, how identity is verified at every step, and how we can gracefully degrade functionality under attack to preserve essential operations. By designing for containment, observability, and resilience from day one, we transform the core into a fortress that evolves with the threat landscape, rather than a brittle shell waiting to be cracked.
Cost-Efficient Evolution: Monetize Your 5G Investment Sooner
Rolling out 5G infrastructure demands substantial capital, but waiting years for a return doesn't have to be the only model. Operators are now rethinking deployment strategies—spreading costs over time by prioritizing high-traffic zones and leveraging existing 4G assets where full 5G isn't yet justified. This phased approach trims initial outlay while still pushing premium services to customers who want them first.
Shared networks and infrastructure-as-a-service partnerships are shifting the financial equation. Instead of each carrier building its own standalone towers and backhaul, collaborative models allow multiple providers to split the expense and accelerate coverage. The result? Faster monetization through expanded reach, without the bloat of duplicated effort. It’s a pragmatic pivot that turns a cost centre into a revenue stream months—not years—sooner.
On the services side, slicing and edge computing open doors to enterprise contracts that pay for themselves quickly. Customized network slices for factories, logistics hubs, or event venues deliver guaranteed latency and bandwidth—features businesses will pay a premium for. By packaging these as managed services rather than raw connectivity, operators can tap into recurring, high-margin income far earlier in the 5G lifecycle.
FAQ
They deliver the central infrastructure that manages subscriber data, authentication, session control, and routing for mobile networks, including hardware, software, and integration services to support voice, data, and emerging services.
It allows operators to scale capacity on demand, roll out new services rapidly, support diverse devices and applications, lower operational costs through automation, and maintain interoperability across legacy and next-generation access technologies.
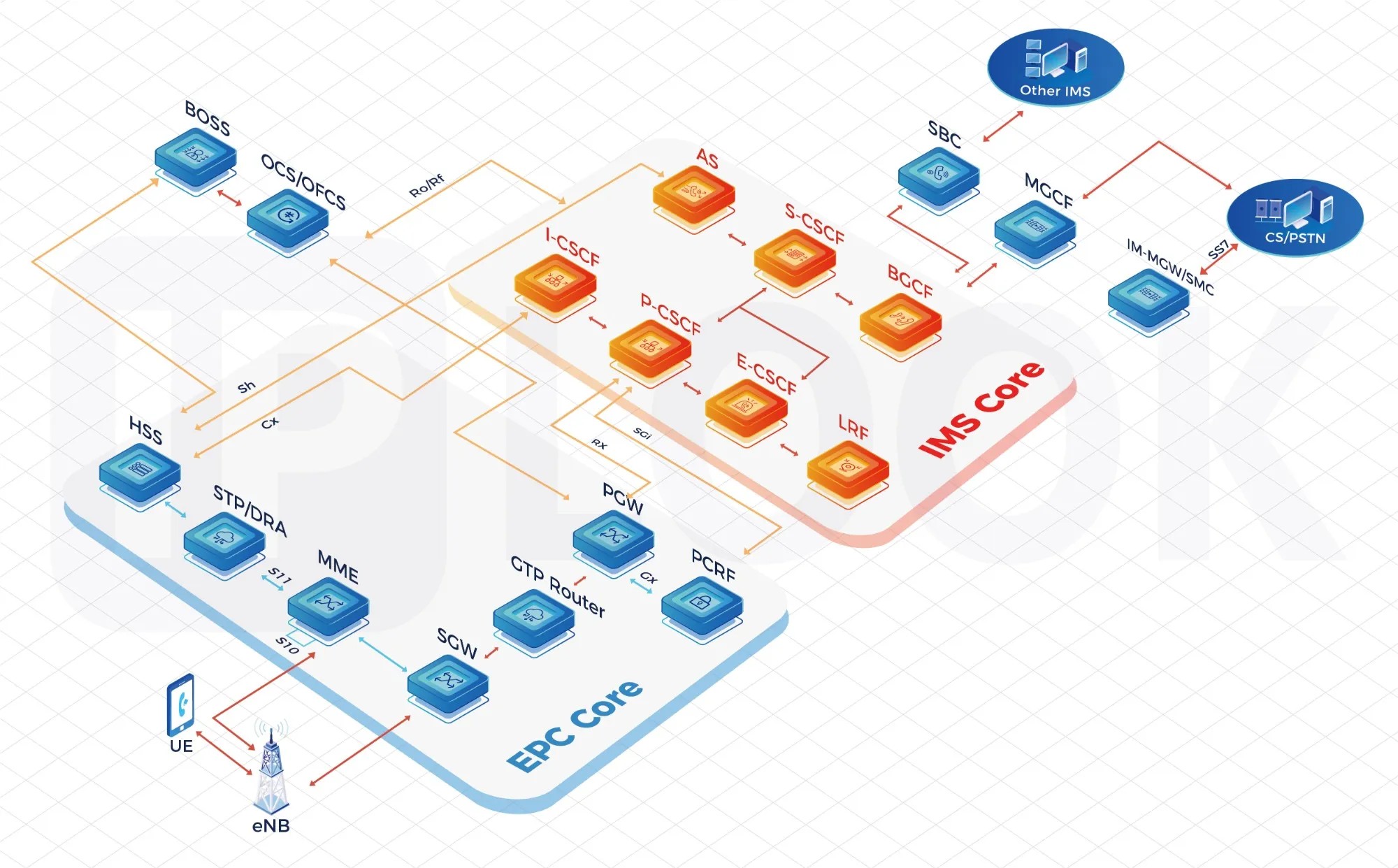
Key technologies include 5G standalone architecture with service-based interfaces, cloud-native network functions, network slicing, edge computing integration, and support for protocols like HTTP/2, as well as legacy 4G EPC elements for fallback.
Traffic patterns, device density, and service expectations evolve quickly; an inflexible core can bottleneck innovation, cause outages, and inflate costs, whereas a ready architecture absorbs shifts like IoT surges or ultra-reliable low-latency needs without major overhauls.
Exceptional providers combine telecom expertise with IT agility, offer open APIs for seamless third-party integration, have proven multi-vendor interoperability, and emphasize automation, analytics, and carrier-grade reliability with continuous delivery pipelines.
Examples include automated lifecycle management of network functions, AI-driven anomaly detection for predictive maintenance, native support for non-public networks, and built-in capability exposure frameworks that allow operators to monetize network assets via APIs.
Conclusion
In an era where mobile network operators (MNOs) face unprecedented data demand, our core solutions go beyond mere capacity upgrades—we architect inherently future‑ready networks designed from the ground up for explosive traffic growth. By embedding 5G‑native integration and cloud‑native agility into every layer, we eliminate the costly growing pains of traditional rip‑and‑replace cycles. Networks built on our platform scale elastically with demand, spinning up resources in seconds rather than weeks, while intelligent automation embeds zero‑touch provisioning, self‑healing, and predictive analytics—turning day‑to‑day operations into a near‑autonomous system that maximizes uptime and frees engineering teams to focus on innovation instead of manual maintenance.
This forward‑looking architecture is reinforced by a security‑by‑design philosophy that hardens the core against tomorrow’s threat landscape, using AI‑driven anomaly detection and a zero‑trust framework that protects subscriber data from edge to core. Critically, we transform network evolution from a cost center into a revenue accelerator: our phased, cost‑efficient migration paths let operators monetize 5G investments sooner, whether through network slicing for vertical industries or ultra‑reliable low‑latency services. The result is a network that not only meets today’s performance benchmarks but actively opens new business models, ensuring that every dollar spent on the core becomes a foundation for sustained competitive advantage in the 5G economy.
Contact Us
Contact Person: Shimmy
Email: [email protected]
Tel/WhatsApp: 85253392231
Website: https://www.iplook.com

